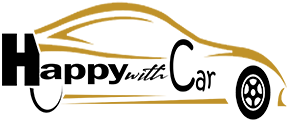
Kaspersky specialists analyzed 69 common third-party cell functions utilized in main linked automobile manufacturers to determine the most important privateness and data safety threats posed to customers.
Tesla, Nissan, Renault, Ford, and Volkswagen automobiles have been recognized as the highest 5 manufacturers which can be most frequently managed by such apps. Kaspersky’s researchers discovered that almost all of those apps fell quick in guaranteeing customers’ privateness and safety.
Greater than half (58%) of the functions did not warn customers concerning the dangers of utilizing the proprietor’s account from the unique automaker’s service. The issue with utilizing non-proprietary apps is that some builders use an authorization token to validate the consumer – versus consumer identify and password authentication – is that if a token is compromised, malefactors can get entry to the automobiles the identical means they’d through the use of victims’ credentials.
This will increase the danger of shedding management over the linked car. Solely 19% of builders have been discovered to appropriately warn the consumer of the danger concerned.
Regardless that most automobile producers have their very own reputable functions for the automobiles they make, third-party apps designed by cell builders are additionally highly regarded amongst customers as they could supply distinctive options that haven’t but been launched by the car producer.
One other key discovering was that one in 5 functions didn’t have data on tips on how to contact the developer or give suggestions, making it not possible to report an issue or request extra data on the app’s privateness coverage. The knowledge is regarding as most of those apps are developed by fanatics and are due to this fact not liable to make sure car security and information safety like regulated car producers are.
Regardless that most automobile producers have their very own reputable functions for the automobiles they make, third-party apps designed by cell builders are additionally highly regarded amongst customers as they could supply distinctive options that haven’t but been launched by the car producer.
What makes these apps much more common is that they’re both freed from cost or supply a demo mode – 46 of the 69 functions fall on this class. The recognition has contributed to such functions being downloaded from the Google Play Retailer greater than 239,000 occasions.
Sergey Zorin, Head of Kaspersky Transportation Safety says that when downloading a third-party software to manage a automobile remotely, customers ought to concentrate on attainable threats. “We entrust quite a lot of non-public data and private information to linked know-how. Sadly, not all builders take a accountable method in relation to information storage and assortment, which leads to customers exposing their private data,” he explains.
Zorin warns that cybercriminals won’t solely steal information and private credentials to promote on the darkish net but in addition acquire entry to the car – and that will result in bodily threats as nicely.
Mitigating threats posed to linked automobiles
For software builders, Kaspersky specialists advocate adopting options that safe the software program improvement course of by software management at runtime, scanning for vulnerabilities earlier than deployment, routinely conducting safety vetting of containers, and anti-malware testing of manufacturing artifacts.
With provide chain assaults by public repositories turning into extra frequent as of late, researchers underline that the event course of is in want of enhanced safety towards exterior interference.
For customers, Kaspersky recommends:
- Downloading apps from official shops just like the Apple App Retailer, Google Play, or Amazon Appstore. Though researchers admit that apps from these markets are usually not 100% failsafe, they a minimum of get checked by store representatives and have some filtration system in place – this implies not each app can get into these shops.
- Checking the permissions of the apps in use and thoroughly assessing earlier than allowing a course of – particularly in relation to high-risk permissions equivalent to entry to accessibility companies.
- Adopting a dependable safety resolution to assist detect malicious apps and adware.
- Updating the working system and all software program usually. Many questions of safety, researchers level out, could be resolved by putting in up to date variations of software program.